Ransomware Report
You can check the latest ransomware information.
- title
- Vgod Ransomware
- Registration date
- 2026-04-08
- views
- 239
Vgod Ransomware Analysis (WhiteDefender)
1. Overview
Vgod ransomware runs on Windows systems and encrypts files, adding an extension in the form of [filename.extension.Vgod] . After encryption, it creates a ransom note called Decryption Instructions.txt and changes the desktop background to the "YOUR DATA IS ENCRYPTED" message to notify the user of the ransomware infection.
Ransomware Information Summary
| item | detail |
|---|---|
| Ransomware names | Vgod |
| Changed extension | Vgod |
| ransom note | Decryption Instructions.txt / Desktop Guide |
| Attacker contact information (based on notes) | vgod@ro.ru |
Sample identifier
| item | detail |
|---|---|
| Size | 2.35 MiB |
| Type | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5 | b0242990818149de592f1dea3f7eb085 |
| SHA1 | 1df73fb6562cce58700ff3edd869023253682a74 |
| SHA256 | 241c3b02a8e7d5a2b9c99574c28200df2a0f8c8bd7ba4d262e6aa8ed1211ba1f |
| SHA512 | d9861e756778ef3e13219ea4d8c8f674a924323aa4d86655faab65aa6f1460e7a6f24de8fb5f32c2174dd6af4f274b876c6777621466be9c3564770dadf0f45f |
| CRC32 | 86e2d5fb |
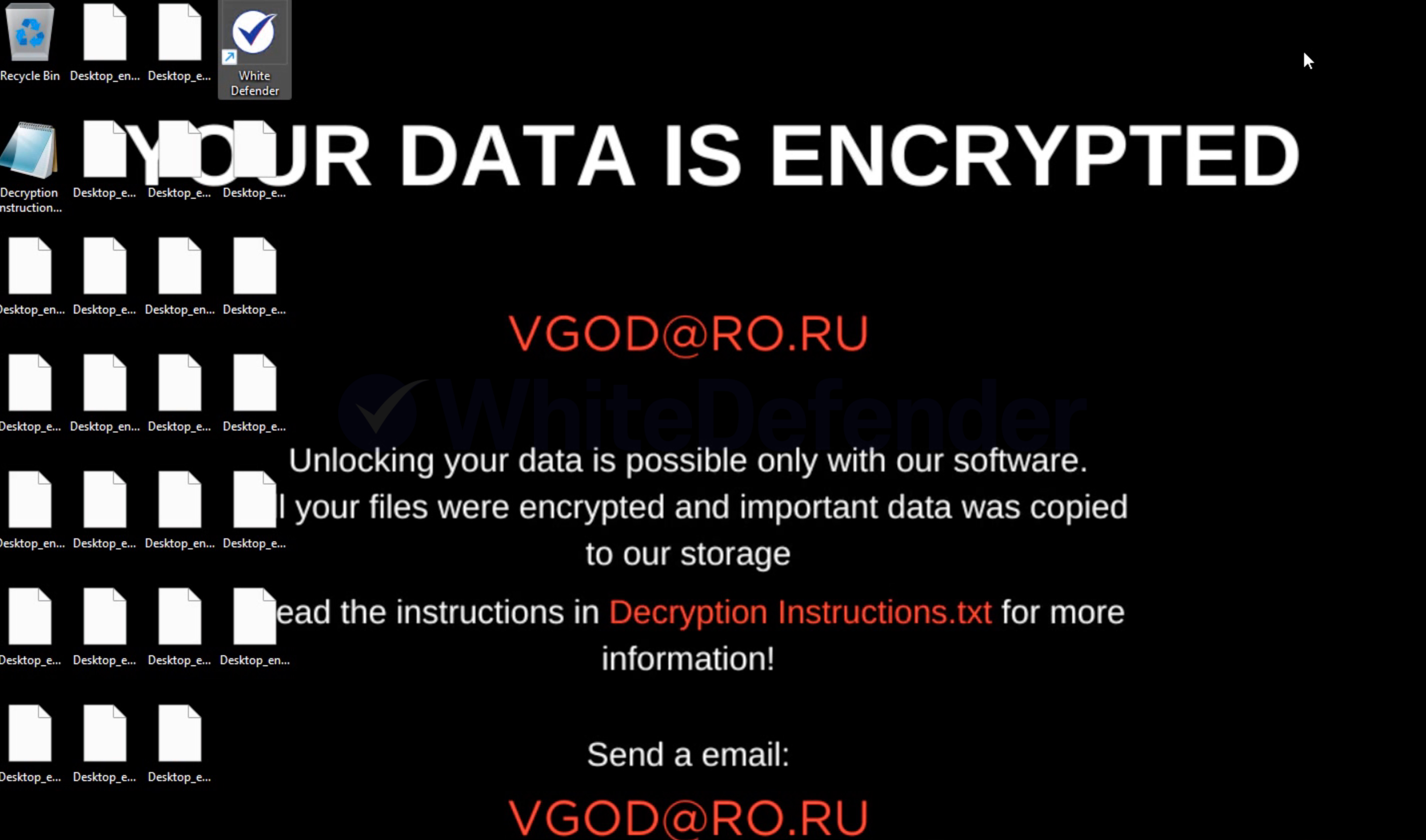
Figure 1. Desktop screen changed after Vgod infection
2. Characteristics of Ransomware Operation
Vgod ransomware encrypts local files immediately after execution, and allows users to instantly become aware of the infection by generating a ransom note and changing the desktop background while encryption is in progress.
Based on the results of this test and observation, Vgod.exe executes from the Documents folder path and simultaneously attempts file encryption and generates a ransom note. Its behavioral pattern is characterized by a concentrated occurrence of high-volume file writing and renaming—specifically, encryption and extension changes—within a short period.
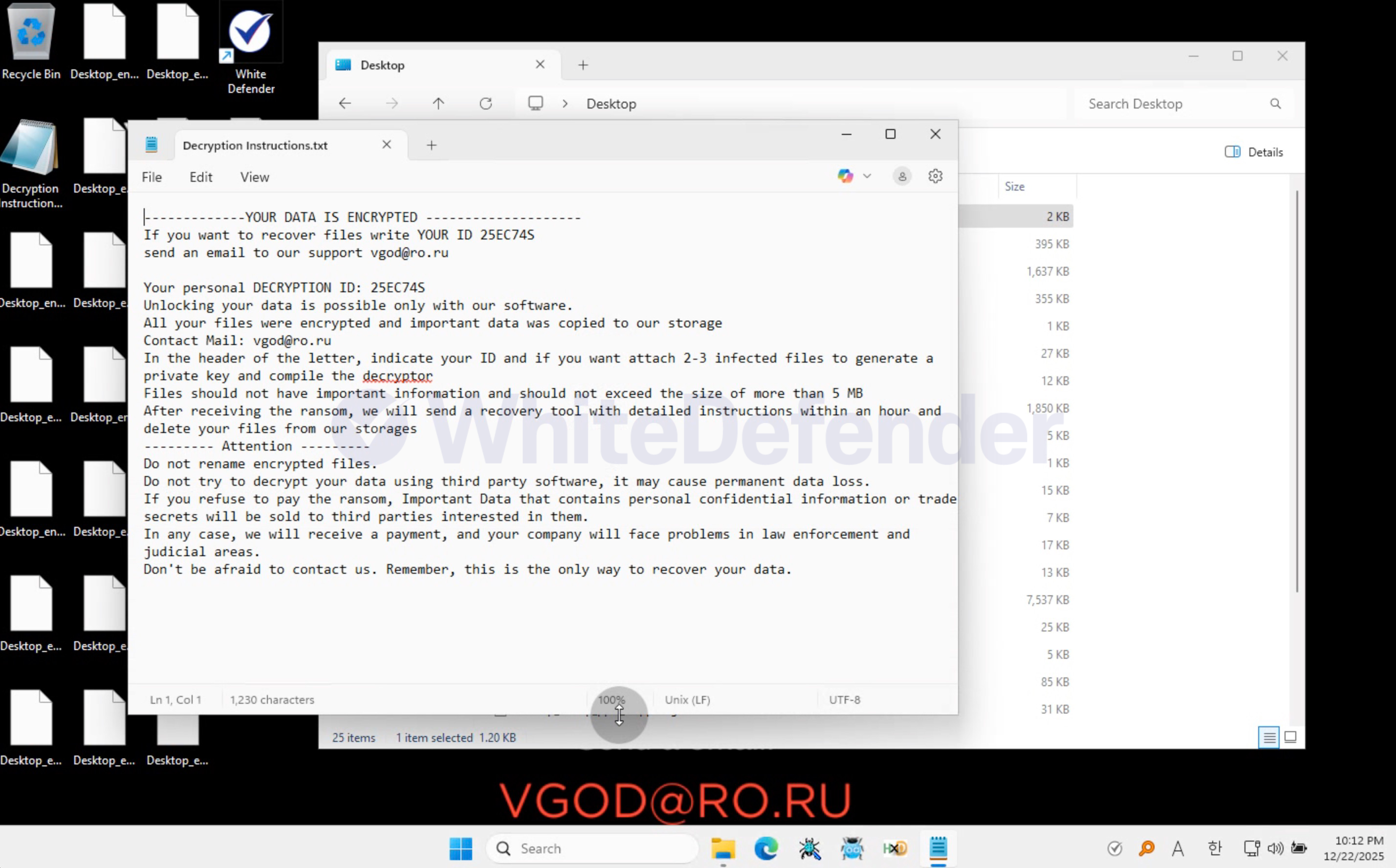
Figure 2. Screenshot of the contents of the Vgod ransom note (Decryption Instructions.txt).
3. Ransomware Infection Results
When a ransomware infection occurs, encryption is performed, a ransom note is generated, and the extensions of each encrypted file are changed, rendering them unusable.
- Files, including major documents and images, have been changed to the .Vgod extension and cannot be viewed.
- Create Decryption Instructions.txt ransom note
- Desktop changed to a ransom message
- You can find a request to contact via email ( vgod@ro.ru ) and threatening messages in the ransom note.
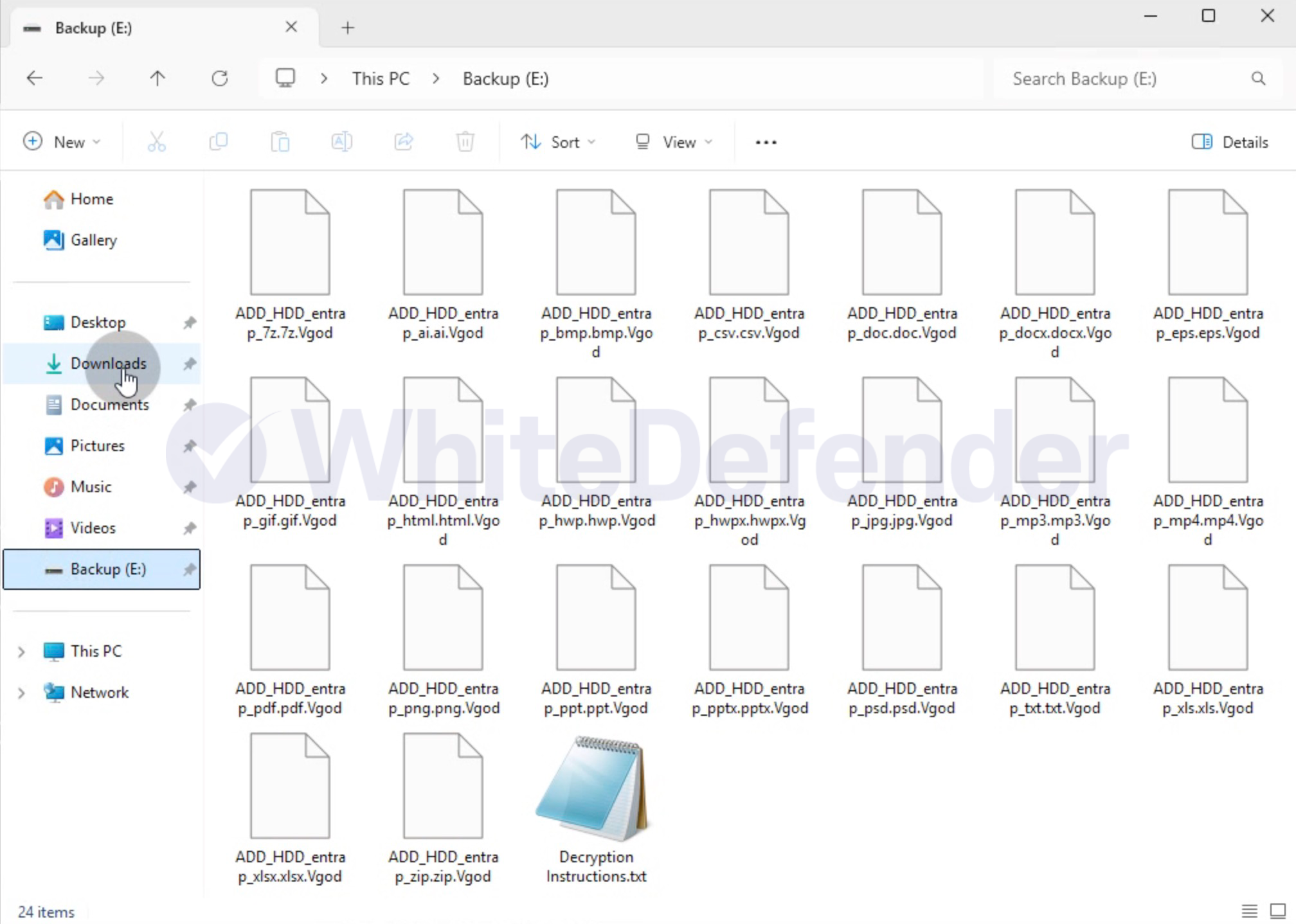
Figure 3. Example of encrypted file extension (.Vgod) changed after Vgod ransomware infection
4. WhiteDefender Support
Based on the Detect Viewer log (Figure 4), WhiteDefender identified signs of Vgod's file encryption using Ransomware Behavior-Detect and blocked the execution of Vgod.exe using Execution Block . Subsequently, Quarantine and Restore results were recorded for file change events, confirming that blocking and damage minimization measures were performed simultaneously.
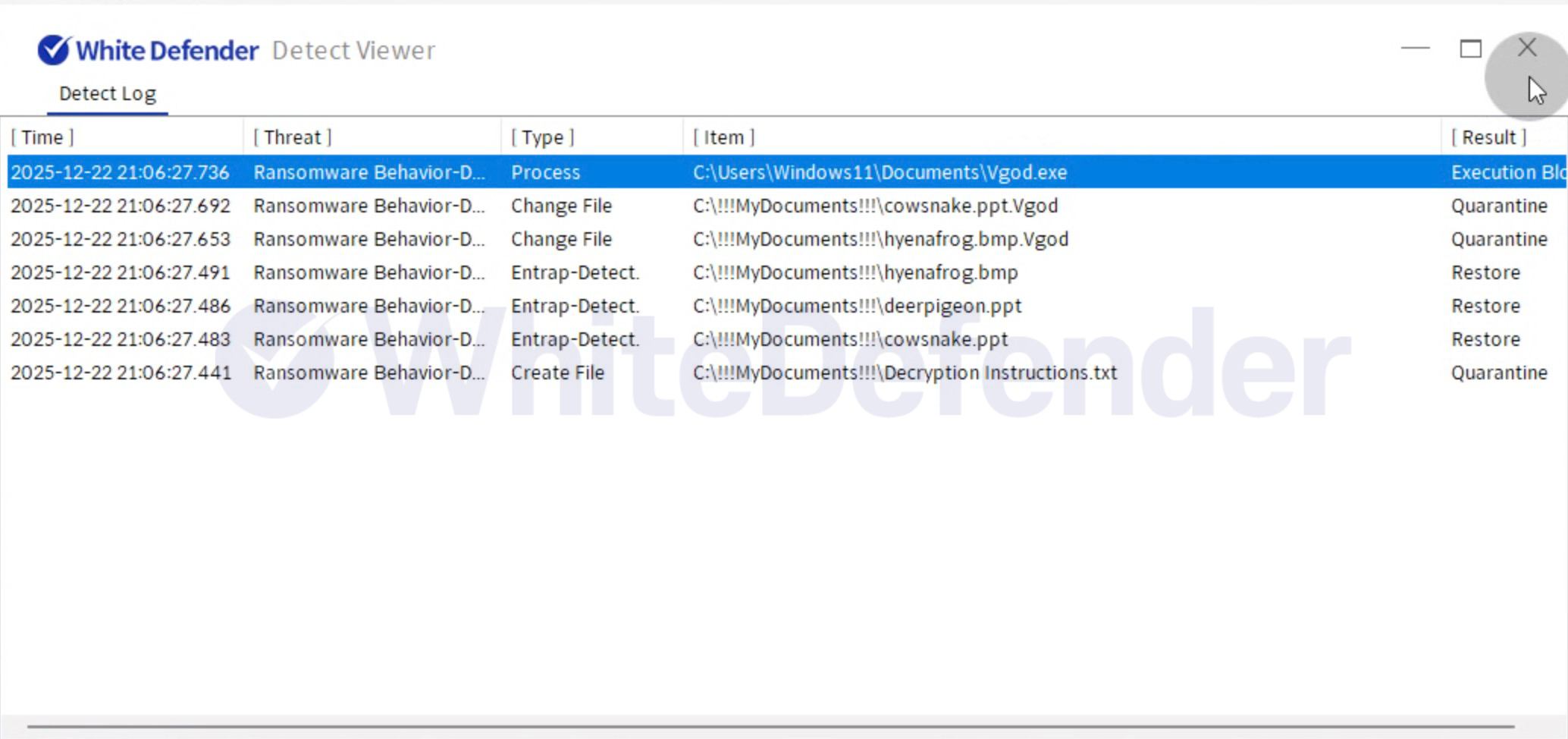
Figure 4. WhiteDefender Detect Viewer Detection Logs: Ransomware Behavior-Detect Detection and Execution Block / Quarantine / Restore Records
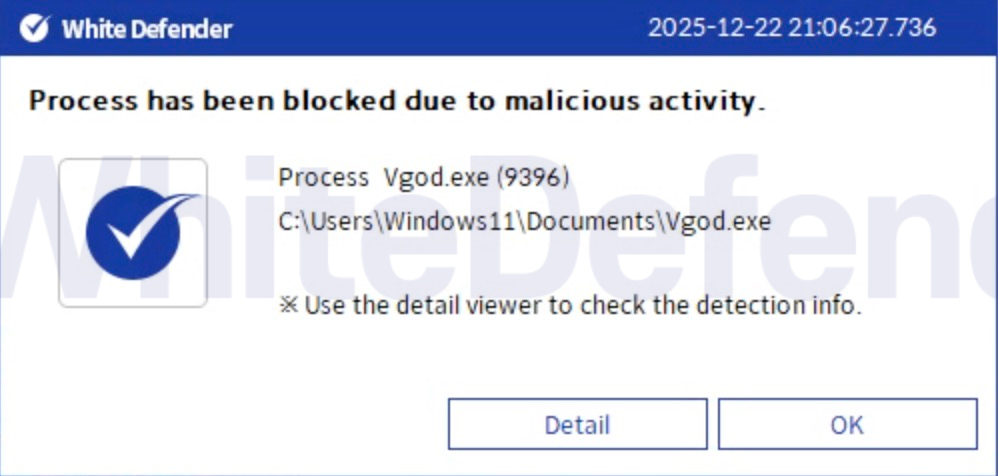
Figure 5. WhiteDefender Blocking Notification Popup: Process has been blocked due to malicious activity (Vgod.exe)

- Previous post
- No previous posts
- next post
- Pandora Ransomware

